RMM software (remote monitoring and management software)
What is RMM software?
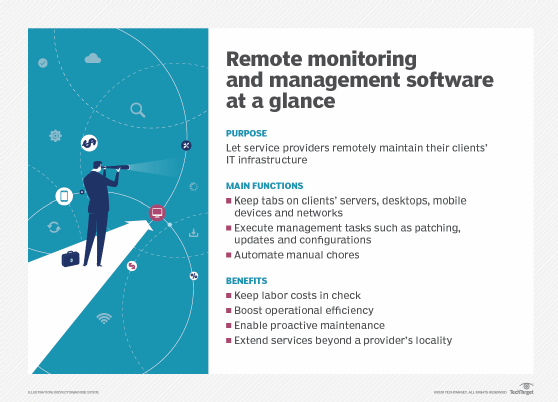
RMM software (remote monitoring and management software) is a type of application that information technology (IT) service providers and departments use to maintain their clients' and business organizations' IT assets, infrastructure and systems. The software is a key management tool for managed service providers (MSPs), in particular, whose business model is based on the ability to deliver IT support services remotely. Other businesses use those same capabilities to monitor their IT systems and networks locally and remotely, while also delivering administrative services.
An RMM platform is one of several IT management and business operation products a channel partner might use to run its business, or a user can deploy to manage its IT operations. The technology has steadily improved to the point that it can be deployed in almost any kind of IT organization to provide administrative services, such as help desk support, real-time identification of vulnerabilities, workstation monitoring, problem diagnosis and management, patch management, IT operations downtime minimization and antivirus software installation.
Several vendors target channel partners with RMM software products. Some are standalone products, but vendors also offer remote IT management as part of a broader, integrated package of offerings for automating an MSP business. RMM systems can be cloud-based or on-site. Systems range from simple open source products to complex multi-tier applications.
Functions of remote monitoring and management
RMM software products offer a variety of tools that assist with the following functions:
- Connects networks and devices. RMM software establishes linkages with networks and devices on those networks.
- Provides monitoring and diagnostic activities. RMM software helps service companies monitor their client systems, including client endpoints such as servers, desktops, applications and mobile devices. RMM agents capture performance data from each infrastructure element and send it to the host for analysis.
- Executes administrative functions. In addition to endpoint device and network monitoring, service providers and end users use RMM to execute management tasks, such as patch management, software updates and new service configurations, on systems and networks. These functions can be executed locally and remotely, a benefit to MSPs with multiple clients and IT departments with complex infrastructures.
How to get started with RMM software
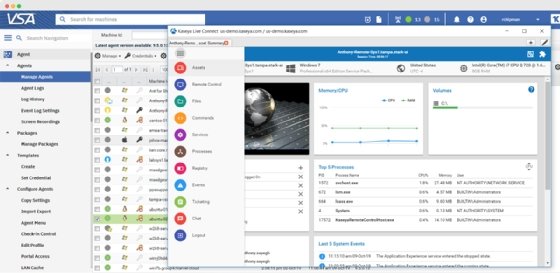
Once the RMM platform has been installed, a service provider or IT team must install agent software on the servers, desktops, mobile devices and network elements. The agent collects data on the monitored devices' health and status, and reports that information to the RMM product's portal, dashboard or console. The MSP or user system administrator can use the product's interface to observe and manage the infrastructure.
RMM software vendor management dashboards provide a single-pane-of-glass view of the IT service company's portfolio of clients as well as the IT department's infrastructure elements. This centralized dashboard displays details such as the number of client or user devices and cloud services, as well as open help desk tickets and alert tickets for each customer and user.
Typically, RMM software will automatically detect devices on client networks. Once devices are discovered, the software automatically onboards and configures them. Most device operating systems (OSes) support RMM apps, including Windows, Linux and macOS devices, as well as Android and iOS mobile devices.
RMM software agents are usually installed on devices that have an OS. For network devices, such as switches and routers, that don't have an OS, RMM software can offer network device management capabilities via the Simple Network Management Protocol.
RMM use cases
RMM software is key to running an MSP business because it enables service providers to keep labor costs down and operate efficiently. Furthermore, because MSPs can serve their clients remotely, they can reduce the amount of time spent visiting customer sites. The same capabilities are true for IT departments as they manage their infrastructures.
RMM products can automate manual processes, such as run check disk. They can create customer scripts to automate a variety of tasks. Automation and scripting address IT infrastructure issues before clients become aware of them, letting MSP and IT professionals do proactive maintenance tasks for customers or on site.
In addition, MSPs can use RMM software to acquire and manage clients that are located outside of their local markets. IT departments can perform similar tasks, such as when a company opens a new office or relocates an existing one.
Benefits of RMM software
The functions and use cases of RMM software translate into several benefits for MSPs and IT departments. Those include, but aren't limited to, the following advantages:
- Creates the technology foundation for offering managed services.
- Establishes a centralized facility for administrative management.
- Improves MSP and IT department employee productivity.
- Reduces costs and increases profitability through labor savings.
- Cuts down on repetitive or redundant activities through automation.
- Improves ability to provide remote support to more clients and larger IT environments.
- Streamlines opportunities to standardize business processes and workflow; this can support the standardizing of IT operational practices.
- Facilitates greater predictability and efficiency in service delivery.
- Improves discovery and detection of operational disruptions, often before they occur.
- Captures performance data that can be used to show how well the MSP or IT department is managing operations. Performance data can be turned into reports and evidence that can be used during IT audits and demonstrate compliance with policies, standards and regulations.
Risks of RMM software
Conversely, the variety of RMM products and services available means users must do careful due diligence when selecting an offering. Pricing varies with each MSP and software vendor. Requirements must be carefully defined before making a selection. If possible, see if a test system can be installed to try before buying.
One risk to consider is that MSPs typically connect to many client infrastructures. Unless security is tightly controlled by both the MSP and client, hackers may be able to sneak in through the MSP's links to its customers.
RMM software vendors
RMM software vendors are many and varied. Products are standalone or cloud-based and often are part of a package of MSP services. IT departments can acquire them as part of their operational strategies. Open source products deliver RMM functionality to small- to medium-sized businesses at minimal to no cost.
A sampling of companies that provide RMM software includes Atera Networks, Auvik Networks, Barracuda Networks, Comodo One, ConnectWise, Datto, ITarian, Kaseya, LogMeIn, Naverisk, NinjaOne, Pulseway and Syncro.
History of RMM
When the MSP business model emerged in the late 1990s, service providers initially used a combination of homegrown tools and data center management products to manage customers' environments. However, software purpose-built for MSPs began to replace earlier automation efforts. The arrival of early RMM products, some built and commercialized by the MSPs themselves, coincided with the evolution and increasing maturation of MSPs from 2000 to 2005.
RMM software enabled the MSP business model, which relies on remote service delivery and remote access to generate recurring revenue streams. RMM, along with other key software components such as professional services automation (PSA) and unified endpoint management, remain the key technology underpinnings of many MSP businesses. In IT departments, RMM software provides an efficient, proactive resource for managing administrative aspects of the organization.
RMM and PSA
MSPs often deploy RMM and PSA products to run their operations. PSA manages essential business processes within an MSP, playing a role parallel to enterprise resource planning systems in manufacturing firms and other types of enterprises. PSA products handle tasks such as project management, resource management, and time and expense management. They're important resources for end-user organizations.
Integrating RMM and PSA can improve MSP and end-user workflow. For example, when the RMM solution encounters an issue in a customer's network, a ticket is generated and routed through the PSA to an MSP or IT technician for resolution. Several MSP software vendors offer integrated product suites encompassing RMM and PSA software.
Some MSPs, however, prefer to purchase what they perceive as the best tools within the RMM and PSA product categories. Those MSPs typically rely on vendor provided integrations to link products together. Integrations not only let MSPs link RMM with PSA, but they also provide gateways to other tools such as backup and disaster recovery offerings and cybersecurity products. Cloud service providers, such as Microsoft Azure, Amazon Web Services and Google Cloud also offer RMM services as part of their many offerings.
MSPs make broad use of RMM tools. Check out these tips on what tools and processes MSPs can use to improve marketing and sales, and better serve their customers.





