
zhu difeng - Fotolia
Learn the ins and outs of Hyper-V containers
Hyper-V containers, which are secure and lightweight in nature, can be managed using the Docker command line or PowerShell and are best suited for stateless applications.
Before you deploy any technology in your production environment, you must understand how the underlying components operate. For example, Hyper-V containers work differently than Hyper-V VMs, in part because the architecture is different. Once you understand Hyper-V container architecture, you can incorporate both instance types in your environment and place workloads depending on application and business needs.
Many organizations still use Windows as their main production OS. Also, many line-of-business applications are designed to work on Windows OSes. You can use Hyper-V to create and run multiple container instances concurrently on a Hyper-V host. Each container runs inside a VM, which provides the isolation between each Hyper-V container and the host machine that Hyper-V container runs on. This is one of the biggest benefits of using Hyper-V container technology, because isolation is provided at the kernel level.
Underlying components
Microsoft relies on Docker Engine to create containers. In other words, Microsoft Hyper-V uses Docker components to create a container environment for Hyper-V. The Hyper-V container provides strong isolation. If you must separate a group of VMs from the rest of your VMs, you could use isolation methods, such as creating virtual LANs and/or creating a separate Hyper-V virtual switch. Hyper-V containers operate differently. The Hyper-V containers you create on a Hyper-V host hold a copy of the Windows kernel mode, but the system assigns memory directly to the container. Since the isolation is at the kernel level, Hyper-V containers provide service providers an environment to run untrusted and multi-tenant applications on the same Hyper-V host. In other words, the Hyper-V host and Hyper-V containers are running in their own kernel spaces.
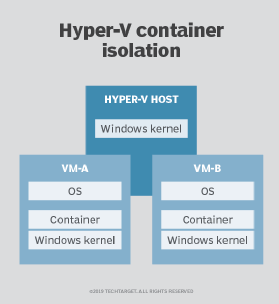
As you can see in Figure 1, the Hyper-V host is running two VMs, and each VM is running a Windows OS. When you create a container inside the VM, the process implements a separate Windows kernel for each VM.
Hyper-V containers support almost all enterprise-level features, such as scheduling, health monitoring, failover clustering, scaling containers and networking between containers, as well as between containers and applications.
Hyper-V container management
There aren't as many tools to manage Hyper-V containers as there are to manage Hyper-V VMs. The Docker command-line tool is the primary one. Microsoft also put a lot of effort into building a module to manage Hyper-V containers using PowerShell. Apart from using the Docker command line and PowerShell, many vendors have also designed GUI management tools to manage containers deployed in your environment. Ossisto 365 Active Directory Health Profiler can actually perform a health check of Hyper-V containers and report their status.
To create a container using the Docker command line, use the command below:
docker run -i --isolation=hyperv microsoft/nanoserver cmd
To create a container using PowerShell, use the New-Container cmdlet as it's shown in the script below:
$HVContainer = [Docker.PowerShell.Objects.IsolationType]::HyperV
$ImageName="windowsservercore"
$container = New-Container -Id "$ImageName" -Isolation $HVContainer -Command @("cmd", "/c", "echo Worked")
$container | Start-Container
$container | Wait-Container








