
WavebreakmediaMicro - Fotolia
12 Microsoft Exchange Server security best practices
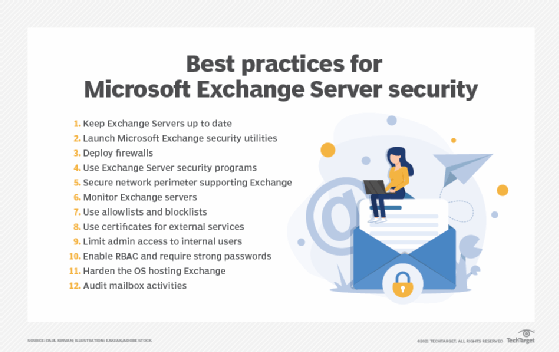
Exchange security has come under increased scrutiny since the recent exploitation of critical vulnerabilities. Review this list of activities to best protect your enterprise.
Microsoft Exchange Server is a widely used email server application. Many utilities, as well as supporting tools and aids, have been developed for it. Considering how important email is to any organization, maintaining a secure Exchange server is an essential activity.
Zero-day vulnerabilities on Exchange Server -- not Exchange Online -- that were exploited by cyber attackers starting in January 2021 have put the server's security in the spotlight. While the remote code execution exploits can be mitigated by deploying Microsoft patches and updates, it is still critical for security teams to pay close attention to other Exchange security best practices.
IT professionals should use the following 12 activities to secure and protect Exchange servers from unauthorized access, cyber attacks, viruses and malware.
1. Keep Exchange servers up to date
Microsoft regularly releases software updates, patches and other resources to keep Exchange servers running at peak performance. Ensure Exchange Server maintenance includes deployment and testing of updates, builds, patches, bug fixes, security updates and feature compatibility.
2. Launch specialized Microsoft Exchange security utilities
Microsoft offers an array of tools to ensure Exchange is secure and performing normally, including the following:
- Microsoft Exchange On-Premises Mitigation Tool. Recent cyber attacks on Exchange servers necessitated the creation of this simple-to-use automated tool that meets the needs of users using current or out-of-support versions of on-premises Exchange Server. Downloading and running the tool mitigates the recent zero-days on any Exchange server on which it is deployed. While it is not a replacement for regular Exchange security updates, it is an expeditious way to mitigate risks to internet-connected, on-premises Exchange servers prior to patching.
- Microsoft Safety Scanner. Also known as Microsoft Support Emergency Response Tool, this downloadable scanning tool finds and removes malware from Windows systems, including Exchange.
- Microsoft Defender Antivirus. This Windows antimalware tool automatically mitigates the recent zero-days. It also scans the server and reverses changes made by known threats.
- Microsoft Security Configuration Wizard. This tool analyzes the OS supporting Exchange 2008 and recommends ways of enhancing security.
- Microsoft Security Compliance Toolkit. This toolkit analyzes, tests, edits and stores Microsoft-recommended security configuration baselines for Exchange Server, comparing them against other security configurations.
- Exchange Analyzer. This PowerShell tool examines the current Exchange environment and compares it to Microsoft best practices to identify modifications that can be made to improve its security posture.
- Microsoft Exchange Online Protection. This cloud-based filtering service protects against and removes spam, malware and viruses in emails. It is included in all Microsoft 365 installations using Exchange Online mailboxes. It can also be supported by hybrid installations using on-premises and cloud-based mailboxes.
- Microsoft Exchange antispam and antimalware. These functions are supported in Exchange 2016 and 2019. Antispam protection is provided by the same built-in transport agents that were introduced in Exchange Server 2010. Antimalware protection is provided by the malware agent that was introduced in Exchange Server 2013.
3. Deploy firewalls
Exchange Server can use Windows Defender Firewall with Advanced Security to facilitate the passage of Exchange traffic. Third-party firewalls designed for Exchange are also available and may include functions to address potential cybersecurity threats, such as viruses, worms, spyware and spam. When evaluating third-party firewalls, check their support features for the Exchange Server version used.
4. Use Exchange Server security programs
Security companies such as Symantec and Kaspersky offer security programs for Exchange Server. Such products protect Exchange from viruses, phishing, denial-of-service attacks, malware and spam. Symantec Mail Security for Microsoft Exchange, for example, also prevents the spread of email-borne threats and enforces data loss prevention policies.
Be sure to evaluate how well a third-party product integrates with Exchange Server, as well as the frequency of malware updating. As viruses that infect email systems often originate within an organization, do not limit scanning to email entering the system from the outside. Make sure the security software scans all email for malware and other cyberthreats.
5. Secure the network perimeter supporting Exchange
Providing a secure network perimeter is an important Exchange Server security best practice. Techniques to secure perimeters include sender-recipient connection checking, content filtering and the use of reverse proxies and Simple Mail Transfer Protocol gateways. On-premises and cloud-based intrusion prevention and detection systems can also be used to scan inbound and outbound emails. Rules in such devices should include the ability to scan for malware and viruses, as well as inspect attachments.
6. Monitor Exchange servers
Numerous tools are available to monitor the performance of Exchange servers, both from Microsoft and third parties. They are typically configured with sensors that detect abnormal conditions. This is done by setting threshold values for various parameters and triggering alerts when those values are exceeded. Sensors can be configured to monitor Exchange mailboxes, databases, backups, email queues and other email functions. Microsoft offers Azure Monitor -- and currently uses the product in its own IT operations -- superseding its System Center Operations Manager, though SCOM is still available for enterprise use.
7. Use allowlists and blocklists
Outlook's allowlists and blocklists enable users to specify trusted and untrusted senders. The function works with the Exchange server, which initiates a safelist process that works with filtering resources to permit or deny senders listed by the user.
8. Use certificates when dealing with external services
An important security method is the use of SSL certificates for external services, such as Outlook Web Access and Outlook Anywhere. Certificates can be generated by either an internal or external certificate authority.
9. Limit administrative access to internal users
Remote administrative access can open the door to potential security issues. Limit administrative access to Exchange servers to internal users only whenever possible. If remote administrative access is needed, implement multifactor authentication to boost security.
10. Enable role-based access control and require strong passwords
As part of their access management strategy, organizations should enable role-based access control (RBAC), which configures and grants permissions based on rules surrounding employees' roles in the organization and their need to know and perform specific actions. It grants access precisely and based on the principle of least privilege, further minimizing the potential for unauthorized access. The use of strong passwords is an important complement to RBAC and other authentication measures.
11. Harden the OS hosting Exchange
Hardening the OS that hosts Exchange is another effective way to increase Exchange Server's security posture. It can be performed manually or with a variety of OS hardening tools, such as Microsoft Attack Surface Analyzer or Bastille Linux. The process of hardening an OS includes several activities, such as configuring the OS for greater security, updating and patching it regularly, defining policies and rules to securely manage the system, and deleting unnecessary or unused applications and services.
12. Audit mailbox activities
Another way to identify possible security violations is to audit mailboxes supported within an Exchange server. This is performed by examining the logs of all activities performed by users on their mailboxes, as well as those of other employees and administrators who can gain access. Logs are then exported for analysis and identification of possible security breaches.






