Active Directory Federation Services (AD FS)
What is Active Directory Federations Services (AD FS)?
Active Directory Federation Services (AD FS) is a feature of the Windows Server operating system that extends end users' single sign-on (SSO) access to applications and systems outside the corporate firewall.
What does Active Directory Federation Services do?
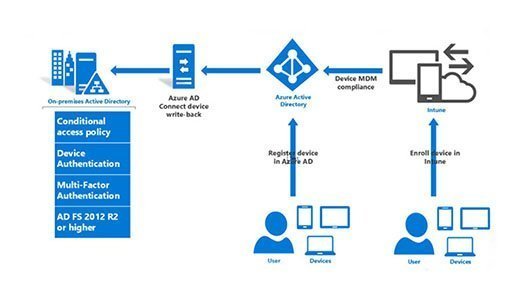
Microsoft's traditional Active Directory technology stores usernames and passwords and uses them to manage and secure access to computers on a Windows domain. It also provides SSO access to corporate applications. AD Federation Services builds upon this functionality to authenticate users on third-party systems, such as another company's extranet or a service hosted by a cloud service provider.
Through SSO capabilities, AD FS can authenticate a user to different, related web apps during a single online session. AD FS shares the user's identity and access rights, also known as claims, across the organization's security boundaries. When users attempt to access a certain web app from one of their trusted business partners -- also known as a federation -- their organization must authenticate the employee's identity information via claims to the host of the web app. The host can then make authorization decisions based on the claims.
Benefits and drawbacks of using AD FS
Active Directory Federation Services aims to reduce the complexity around password management and guest account provisioning, and it has taken on additional importance as organizations and employees rely more on software as a service (SaaS) and web applications. SaaS and web apps typically require their own user accounts, and AD Federation Services ties those usernames and passwords to existing identities. Once a user logs in with his or her Windows credentials, AD Federation Services authenticates access to all approved third-party systems.
AD FS offers benefits to users, IT staff and developers alike. With AD FS, IT can provide sign-on and access control based on a unified set of credentials. Additionally, the feature provides this control across modern and legacy applications, on premises and in the cloud. Users can enjoy a seamless SSO without having to remember unfamiliar, disparate account credentials. AD FS offers developers a simple method to authenticate users with identities in the organizational directory, allowing them to focus their efforts on more important endeavors.
There are a few minor drawbacks to implementing AD FS. It requires additional infrastructure requirements and cost to set up. Like any feature added to an infrastructure, AD FS may add some points of failure.
Important features of AD FS
There are numerous key features that IT teams can take advantage of.
SSO federation
SSO capabilities allow federation partners to share a streamlined experience when they use the organization's web apps. Additionally, IT can deploy federation servers in multiple organizations to enable transactions between federation partners.
Interoperability
Through a federation specification called WS-Federation, AD FS' federated identity management system is interoperable with other products that support web services architecture and even environments that don't use the Microsoft Windows identity model.
Extensibility
AD FS supports the Security Assertion Markup Language (SAML) 1.1 security token type and Kerberos authentication, and can also change claims using a customizable access request. Through this extensible architecture, organizations can adjust AD FS to work with their current security and business frameworks.
Versions of AD FS
Active Directory Federation Services was first released with Windows Server 2003 R2 as an additional download. Since then, Microsoft has released five different versions of AD FS.
AD FS 2.0, Microsoft's third release, is a download from Microsoft.com that is compatible with Windows Server 2008 and Windows Server 2008 R2. Its upgrades include improved installation with new server validation checks, tightened integration with Microsoft Office SharePoint Server 2007 and Active Directory Rights Management Services and an improved experience to establish federated trusts.
In AD FS 3.0 for Windows Server 2012 R2, Microsoft added the possibility to securely register and join mobile devices, support for group Managed Service Accounts and simplified customization of the login platform.
The most recent version, AD FS 4.0 for Windows Server 2016, enables sign-on with Azure multifactor authentication, non-AD Lightweight Directory Access Protocol directories and Windows Hello for Business. Microsoft also improved the auditing process, interoperability with SAML and password management to federate Microsoft and Office 365 users.