Microsoft Outlook on the web (formerly Outlook Web App, OWA)
Outlook on the web is the browser-based email client for users to access email, calendars, tasks and contacts from Microsoft's on-premises Exchange Server and cloud-based Exchange Online.
Outlook on the web provides an interface similar to Microsoft Outlook in the Office Suite without requiring the installation of the full desktop email client. Microsoft named this client Outlook Web App (OWA) when using it with Exchange Server 2010 and Exchange Server 2013. Microsoft also called the browser-based app Outlook Web Access and Exchange Web Connect with earlier versions of Exchange Server.
In 2015, Microsoft changed the browser client name to "Outlook on the web" and updated it for use with Exchange Server 2016 and Exchange Online in Office 365. Outlook on the web offers a well-structured email service with calendar functionality, while providing features such as contact management in the Outlook People page and assignment administration with the Outlook Tasks feature.
Outlook on the web features
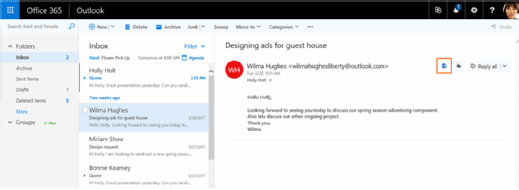
Email: The user interface in Outlook on the web is similar to previous versions of the web-based Outlook client but with newer functionality added in 2015, such as pins, Sweep and image editing.
Pins keep selected messages at the top of the inbox. The Sweep feature handles advanced delete functions, such as deleting all messages from the inbox, automatic removal of future messages from certain senders, keeping just the most recent messages, or retaining just email from the past 10 days. Image features include emoji support and hiding image-based advertisements in preview.
Calendar: Microsoft's updates to Outlook on the web in 2015 added new features to the calendar. There are now multiple options to view the calendar, such as a view for the full week, work week, month and day. Users can share calendars and set up reminders to arrive via email. Microsoft also added a weather forecast feature and new icons for certain events, such as an airplane to indicate a business trip.
People: People is the name of the contact manager in Outlook on the web. Users can search and edit existing contacts, create new contacts and find new contacts through services such as LinkedIn or Twitter. Some advanced functionality includes linking, which joins contacts with the same or alike names as a single contact.
Tasks: OWA introduced the Tasks feature as part of the calendar, but Microsoft converted it to a separate service in Outlook on the web. A user can creates a new task either manually or by flagging an email. The management options include settings for priorities, percentage completed and persons involved in the task. Newer features include adding start and due dates, and rich text editing to boldface type or add bullet points.
Skype: Microsoft integrated Skype for Business to Outlook on the Web to let users initiate free Skype voice and video calls, and see active conversations. A user accesses this feature through the Skype icon on the navigation bar.
Differences in the versions of Outlook
Outlook 2016 on desktop is Microsoft's locally installed application to access Exchange Server or Exchange Online, and has a similar user interface as Outlook on the web.
Both desktop and web versions of Outlook have similar levels of integration with social networks. Outlook and Outlook on the web share similar calendar and mailbox functionalities. Both share similar search functionalities as well, with the exception of Outlook on the web's additional option to view contacts based on importance.
Microsoft drops its Outlook on the web apps
On March 2018, Microsoft released a blog stating it would remove the availability of its Outlook on the web apps for iOS and Android tablets and smartphones in April 2018. The blog indicated the apps would stop working on May 15, 2018. The company wrote in-app users on both operating systems would receive end-of-support notices accompanied by prompts to use the Microsoft Outlook app instead.
The Microsoft Outlook app trails the desktop Outlook client and the Outlook on the web apps in functionality. The Microsoft Outlook app does not have favorite folders, a way to view or send mail from shared mailboxes, or access to Office 365 Groups. The Microsoft Outlook app can't categorize, ignore, clean up, report as junk or mark message lists as clutter. The Microsoft Outlook app can't apply importance levels to new messages or replies, nor can it set automatic replies. The Microsoft Outlook app lacks calendar functionality such as a weather bar, ability to edit responses, calendar sharing and capacity to forward meetings. However, the Microsoft Outlook app supports additional connectivity to accounts such as Gmail, Yahoo, and POP or IMAP accounts. The Outlook app can schedule messages and supports swipe gestures. In addition, it features similar search functionalities to Outlook on the web.






